WHITEPAPER:
Applying Zero Trust Principles to Device Security
Seven Best Practices to Protect Critical IT Resources
Cloud migration and distributed workforces change how organizations need to secure their digital data.
Rapid risk reductions can be achieved by focusing on improving identity management and device security.
This whitepaper outlines seven best practices to protect critical IT resources and accelerate implementation and maturity for Zero Trust device access.

Download the whitepaper to learn:
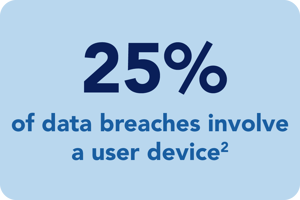
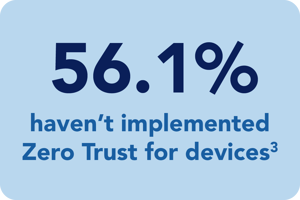
- Why Zero Trust is needed at the device level
- What NIST, DISA, Gartner and Forrester are recommending
- How to integrate user and device authentication into access decisions
- What is required for a great user experience
About Us
Infinipoint is a pioneer in the Device-Identity-as-as-Service security category to extend a true Zero Trust security posture to devices. Infinipoint is the only solution that provides Single Sign-On (SSO) authorization integrated with risk-based policies and one-click remediation for non-compliant and vulnerable devices.
1 Verizon DBIR 2021
2 Verizon DBIR 2021
3 Infinipoint Zero Trust report, 2022
2 Verizon DBIR 2021
3 Infinipoint Zero Trust report, 2022